In the world of global sourcing and procurement, receiving a product that differs from what you ordered—known as an unauthorized substitution—is a significant risk. It can derail projects, damage client trust, and impact your bottom line. Proactive verification is your strongest defense.
The Golden Rule: Verify, Then Trust
The core of prevention lies in establishing a clear, documented checkpoint before
Two-Fold Protection Strategy
Implement these two critical practices to create a robust verification system.
1. Confirm Details Against Master Documentation
Never rely on memory or fragmented emails for final verification. Use a single source of truth.
- Maintain a Master Spreadsheet:
- Systematic Cross-Check:
- Centralize Communication:
- Systematic Cross-Check:
2. Demand and Scrutinize Proof Before Approval
"Proof" must be concrete, specific, and unambiguous. Vague assurances are not acceptable.
- Request Compelling Evidence:
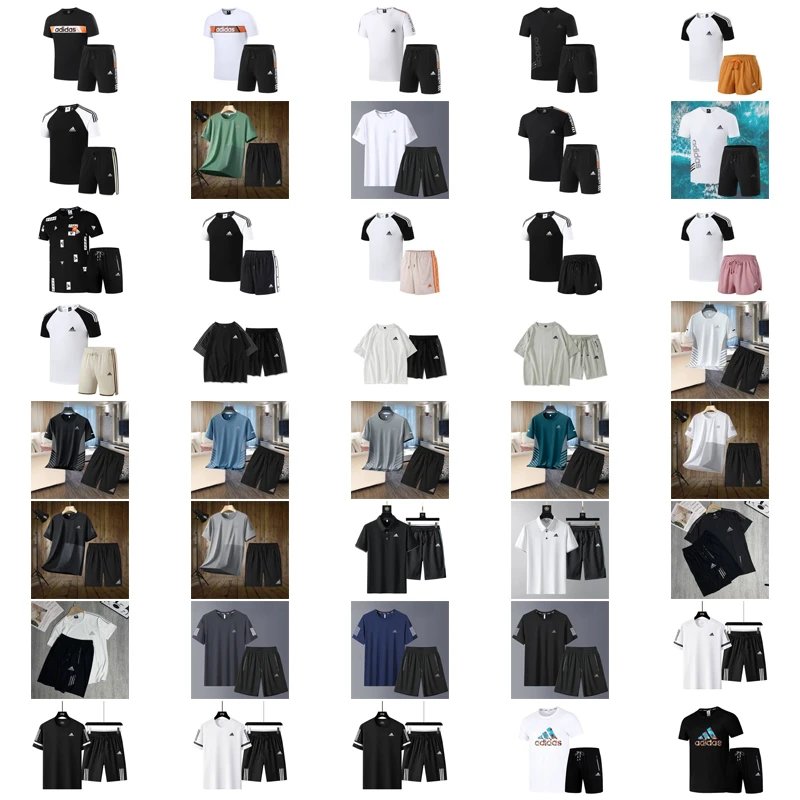
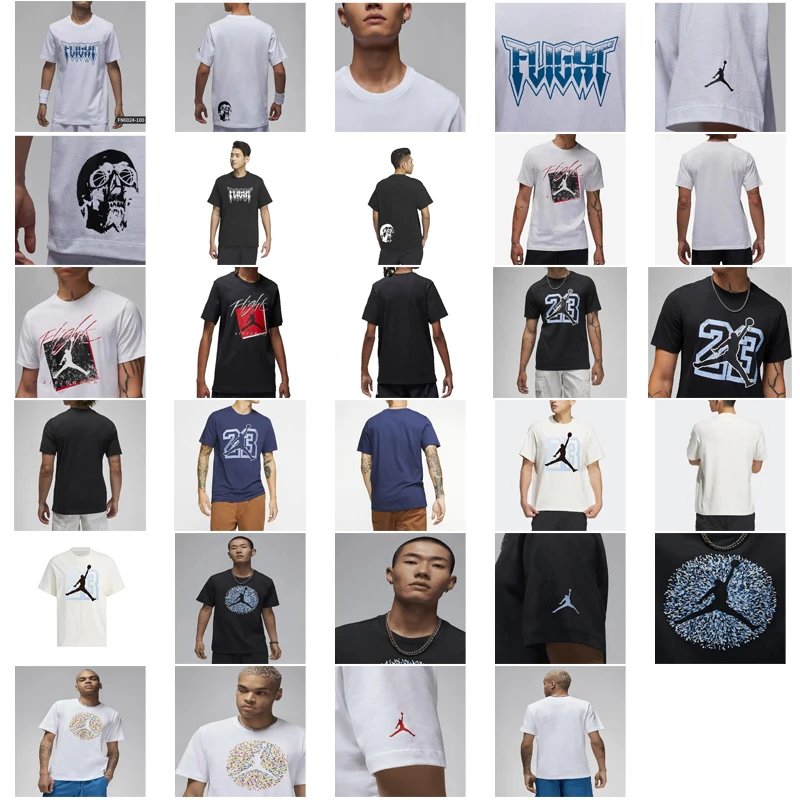
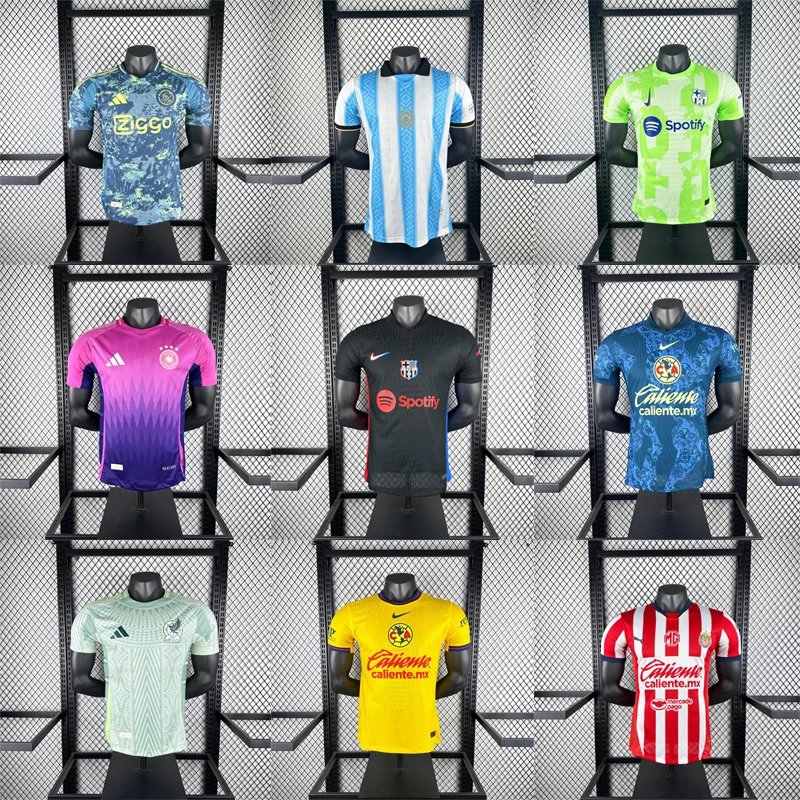
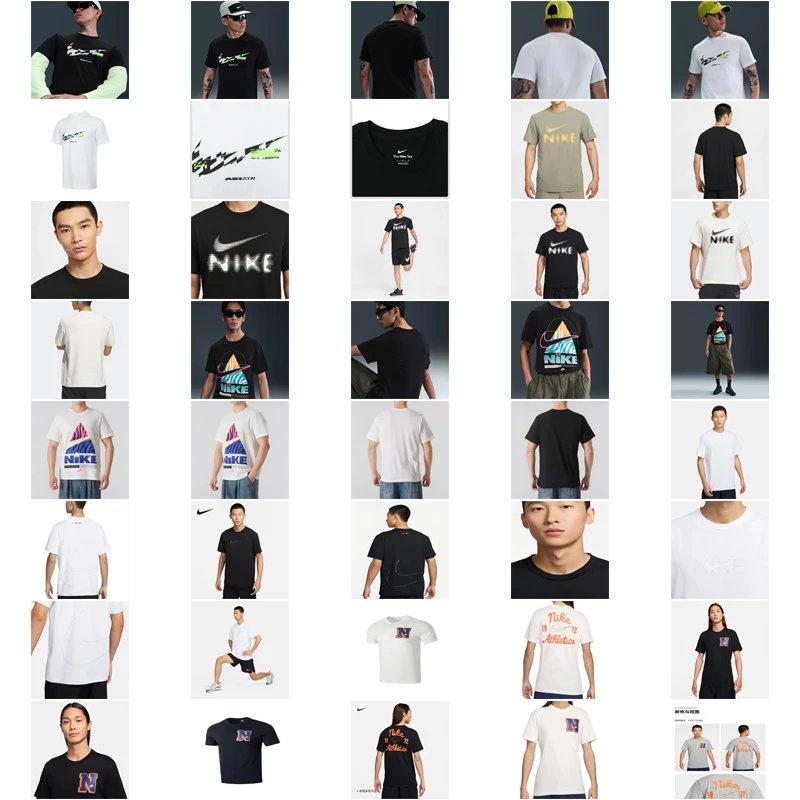
- The final product from multiple angles.
- Critical details (e.g., logos, labels, connectors, fabric texture).
- Measurement checks with a visible caliper or tape measure.
- The packaging and any custom labeling.
Sample Pre-Shipment Verification Workflow
- Supplier Notification:
- Documentation Request:
- Verification:
- Does the color match the Pantone code in Cell D4?
- Is the length as specified in Cell F7?
- Is the logo placement per the diagram linked in Cell G12?
- Action:
- Documentation Request:
Staying Secure
Unauthorized substitutions are often attempts to cut corners or use cheaper materials. By institutionalizing the practice of spreadsheet confirmationpre-shipment proof approval, you transform from a passive recipient to an active quality controller. This diligence protects your business, ensures consistency, and builds stronger, more accountable relationships with your suppliers on platforms like ItaoBuy.